Proxy servers are a fundamental part of modern internet architecture, handling millions of network requests every day. They are used to manage traffic, filter content, balance loads, and control access to resources—both in corporate networks and public infrastructure. In practice, this is facilitated by specialized platforms such as buy proxy, which provide access to different types of proxies depending on business or user needs, allowing flexible configuration and varying levels of anonymity.
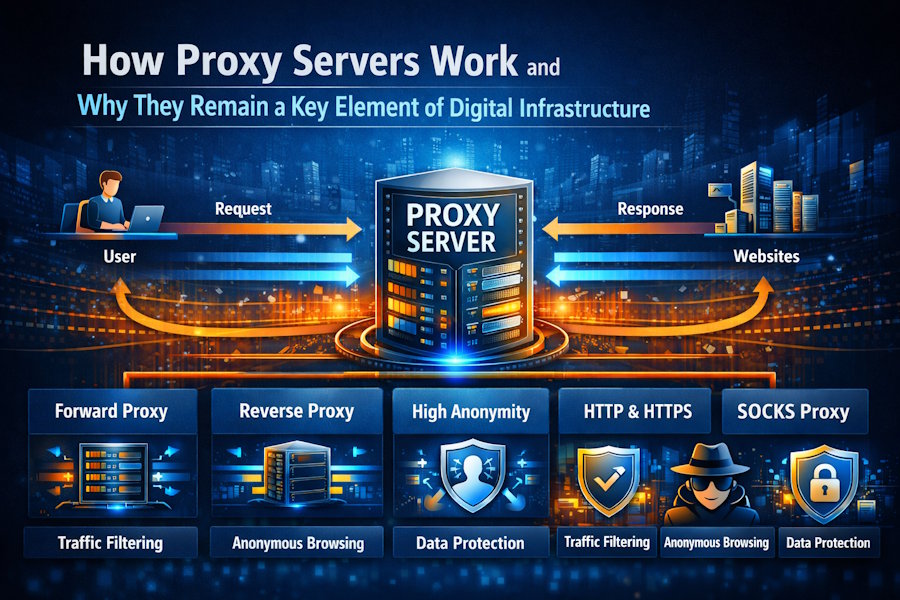
Unlike a direct connection between a user’s device and a website server, a proxy server acts as an intermediary: it receives the request, forwards it to the target resource on behalf of the user, obtains the response, and delivers it back to the client. Depending on its configuration, a proxy can modify network headers, cache content, restrict access, or mask connection parameters. This versatility makes proxies useful not only for performance and security but also for bypassing network restrictions.
Main Types of Proxy Servers
Forward Proxy sits between the user and external resources and handles outgoing requests. It can modify headers, cache content, and control access to resources. These proxies are the most commonly used by individual users and businesses for managing network traffic.
Reverse Proxy operates on the resource side. It accepts requests from users and decides which internal server should handle them. This makes it a key tool for load balancing, increasing fault tolerance, and protecting infrastructure. In most cases, end-users do not even realize they are interacting with a system using a reverse proxy.
In practice, choosing a proxy type depends not only on technical requirements but also on how the infrastructure is managed. Platforms like buy proxy enable centralized control over proxy resources, allowing for load distribution, filtering, and anonymity management, simplifying configuration for businesses and advanced users.
Levels of Proxy Anonymity
Transparent Proxy does not hide the fact that it is being used or the user’s real IP address. It is applied where monitoring and content filtering are more important than anonymity, such as caching data or restricting access to certain resources.
Anonymous Proxy replaces the user’s IP address but does not conceal the fact that a proxy is being used. This makes it harder to link traffic to a specific device, though resources still recognize that the request passes through an intermediary.
Distorting Proxy modifies HTTP headers and the IP address without notifying resources that a proxy is involved. This reduces the risk of exposing personal data and makes behavior analysis more difficult.
High-Anonymity Proxy regularly changes IP addresses and fully masks user activity. Such technologies are also used in corporate ecosystems; for example, Apple employs a multi-layer proxy architecture to protect user data.
Proxy Servers by Protocol
HTTP Proxies remain the most common type. They are used for caching data, speeding up loading, blocking unwanted resources, and filtering ads.
HTTPS Proxies encrypt outgoing traffic, protecting login credentials, passwords, and payment information. However, technically, traffic can be decrypted on the proxy side depending on its configuration.
SOCKS Proxies are considered the most versatile. The protocol was developed by Dave Koblas in 1992 and is now available in versions SOCKS4 and SOCKS5. These proxies do not transmit information about user activity and do not signal to resources that a proxy is being used.
Proxy vs. VPN: Key Differences
Both proxies and VPNs act as intermediaries between a user and the internet, changing the IP address. The main difference lies in encryption.
Proxies handle application-level tasks—filtering, caching, access control, and load distribution. VPNs create a secure tunnel between the device and the server, providing end-to-end encryption of traffic.
Modern proxies, such as Squid, can handle encrypted traffic, but data is often decrypted on the server side. In VPN architecture, encryption is a built-in function rather than an optional feature.
Why Proxy Servers Remain Relevant
For individual users, proxies are attractive because they are simple to set up and do not require additional software.
In corporate environments, proxy servers are used for traffic analysis, preventing data leaks, protecting internal networks, and optimizing load. They provide both confidentiality and access control, remaining a key component of infrastructure alongside VPNs.
Platforms like buy proxy allow companies and professionals to manage proxy resources flexibly, selecting types and anonymity levels to match specific needs—whether it’s filtering, load balancing, or securing corporate data.